The threat of cyber attacks is at an all-time high and growing; the financial implications are continuing to rise as well. Cybersecurity Ventures, a leading research organization of the global cyber economy, predicts that cybercrime damages will cost the world $6 trillion annually by 2021, doubling $3 trillion spent in 2015. Deputy Attorney General Rod Rosenstein referenced this statistic in his remarks at the Cambridge Cyber Summit to illustrate just how critical cybersecurity defense is to the US government. In his 2017 speech, Rosenstein detailed a new type of attack that is more sophisticated and has targeted specific business demanding large payments to undo the attack— ransomware.
Ransomware is now estimated to infect more than 100,000 computers a day around the world and is responsible for more than $1 billion dollars of ransom payments annually according to the FBI. In addition, the United States Computer Readiness Team, or CERT, says “Ransomware is a type of malicious software, or malware, designed to deny access to a computer system or data until a ransom is paid. Ransomware typically spreads through phishing emails or by unknowingly visiting an infected website.” Due to recent spikes in recorded cases and money stolen, this form of attack is still being researched by the US government and private institutions to better understand the threat and how to protect organizations and government entities.
PROTECTING YOUR BUSINESS FROM RANSOMWARE
The FBI has released some tips on prevention and detection of ransomware, with two key responses to the attack. Prevention efforts, including strong technical controls, awareness training for employees and a strong and an updated business continuity plan which includes cybersecurity event recovery. Read more about the FBI’s tips for dealing with ransomware here.
- Having a plan in place to respond to the attack can help mitigate the effectiveness of the attack and can render some aspects of the threat harmless. For example, a common ransomware attack is the theft or hijacking of a system that contains records or trade secrets. If this data is encrypted, the attacker will have a lower probability of recovering the data to use against the company.
- Another key defense, which is part of a business continuity plan, is having up to date backups which are not connected to the same system or production network which is likely to be attacked. If the key threat of ransomware is the theft of records or company data, having a recent backup eliminates the extreme damage caused by those records being destroyed or inaccessible.
Like any other cyberthreat, the threat of ransomware can’t be completely eliminated. Improving awareness, defenses and recovery strategy is the first step towards reducing the likelihood and limiting the impact of the threat.
LEARN MORE
To learn more about Phishing attacks, be sure to read PHISHING—THE NUMBER ONE CYBER ATTACK TOOL.
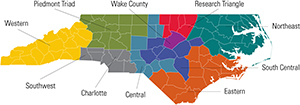
If you are interested in minimizing your cybersecurity risks but aren’t sure how to begin, NC State Industry Expansion Solutions has created a free cybersecurity toolkit which you can download today. Industry Expansion Solutions (IES) is the administrator for the North Carolina Manufacturing Extension Partnership (NCMEP). Or drop me a line to chat more.
SOURCES
Deputy Attorney General Rod J. Rosenstein Delivers Remarks at the Cambridge Cyber Summit
Cybersecurity Research: All In One Place
FBI- Incidents of Ransomware on the Rise
—
Brian Vigna is an Instructional Designer in the Professional Learning and Instructional Design unit for NC State Industry Expansion Solutions (IES). Brian has worked as an Adult Educator, Trainer, and Instructional Designer for more than 7 years. Brian has taught a variety of certification and professional development courses at the collegiate level as well as in collaboration with the United States government.